As far as action-packed hacker movies go, you may be shocked by how many similarities there are between the Hollywood version and what happens in the real world. Despite their stereotypes, the characters’ characteristics aren’t dissimilar to those of real-life hackers and programmers. More action and intrigue are generally found in hacker flicks, which are usually high-risk games that could have deadly consequences. Despite the fact that not all real-life hacking instances are nail-biters, the movie sequences and plots are inspired by what has happened or what is possible.
- 15 Cute Anime Characters That You Should Watching Update 07/2024
- 24 Best Movies Like Sleeping With The Enemy Update 07/2024
- 8 Best Anime Like Say I Love You That You Should Watching Update 07/2024
- 12 Best Viking Movies That You Should Watching Update 07/2024
- 10 Best 90s Horror Movies That You Should Watching Update 07/2024
As techies, we’re certainly the greatest judges of which hacker movies to include in our list, so we had some internal debate and came up with these as the top 10. As a result, we also took time to address what students get right and incorrect about hacking in the real world, as well.
You Are Watching: 10 Best Hacker Movies That You Should Watching Update 07/2024
1. WarGames
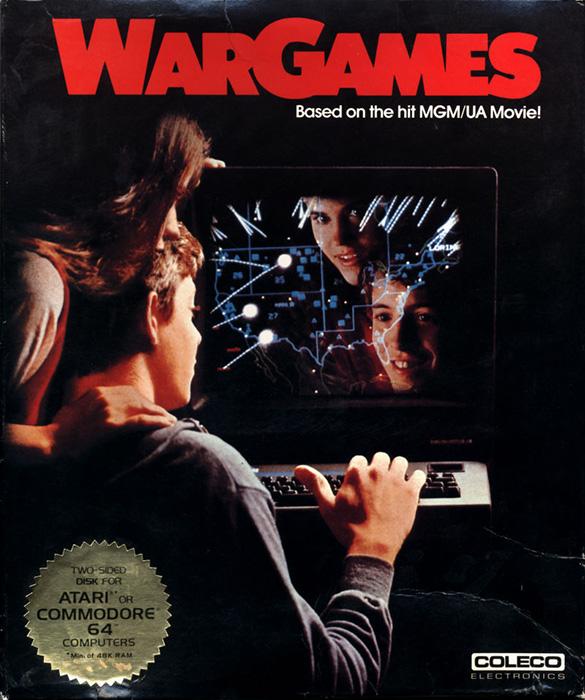
WarGames, which aired in theaters in 1983, was a pioneering hacker film. David, a slacker who happens to be a computer prodigy, is the protagonist of this story. A system that doesn’t identify itself but allows him to play games is discovered while attempting to hack into a computer gaming company. To get around an impasse, he learns of a secret password from others.
A new game will soon begin, yet this is not a game at all. In reality, it’s a nuclear missile launch pad. When the computer system reaches a certain level of intelligence, it develops a strong desire to win. As the software gradually comes to understand, there are no winners in war. The fact that David resembles a typical hacker makes this film a favorite of the hacker movement. Curiosity and intuition are two characteristics shared by many in his field. However, despite David’s sincere desire to learn as much as he could, his curiosity was never completely satisfied.
2. Blackhat
Hackers infiltrate a nuclear plant’s infrastructure and cause it to explode in the first scene of Blackhat. If you’re a blackhatter, you’re breaking into systems for the purpose of gaining money and harassing people. While being sought by two Chinese officers, the Red Hat hacker’s former programming colleague gets released from prison in order to apprehend the hacker before he causes more damage. These three characters all have different perspectives on hacking, but they all have one thing in common: they’ve all been involved in hacking at some point in their lives and they all think they’re either good or terrible.
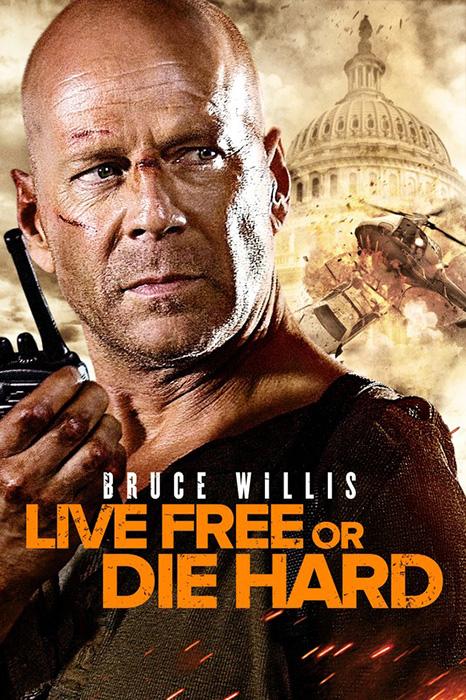
3. Live Free or Die Hard
Read More : 10 Best Short Anime On Netflix That You Should Watching Update 07/2024
“Fire sale” cyber-terrorists who have hacked into government and business computers are now being hunted by the franchise hero, McClane. An article in Wired Magazine by John Carlin entitled A Farewell to Arms shows how breaking into such systems could bring the entire globe to a standstill. Considering how much of the world’s infrastructure is reliant on technology, this film may be the most likely in the hacking genre. Even if the hero isn’t a computer whiz, the movie’s depiction of an infrastructure takeover is convincing enough for him to rely on it.
4. The Matrix
At its core, The Matrix is a hacker film that revolutionized the action genre. When he finally discovers that the world is only a computer program, he is shown as a gifted hacker searching for answers. His goal is to discover the truth about reality as any hacker would, and he discovers that the world as he knows it has been replaced by machines. Nonetheless, the Matrix’s attempt to humanizing robots and making them the antagonist is nothing new. A new way for a hacker to take them out was introduced, though.
5. Sneakers
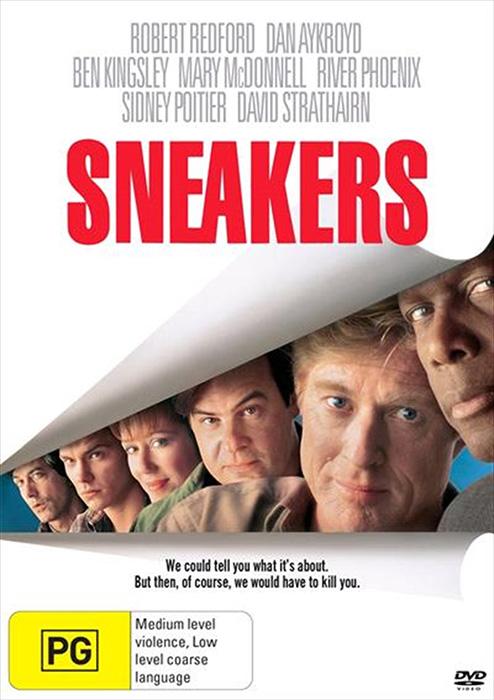
The film’s backstory focuses on the fear of government surveillance, which is a fact. As a gang of security system professionals, they are compelled to steal a government-owned encryption equipment in order to protect themselves from a terrorist attack. If you’ve ever wondered what it’s like to be a “white-hat hacker,” this squad is for you. Even though this video was released in the early 1990s, high-level government surveillance has been shown to be extremely genuine.
6. Hackers
The film Hackers introduced people to the internet before the days of cellphones and Wi-Fi. Hacker Manifesto’s “This is our world today…” is mentioned in the film’s narrative. We’re not criminals, are we? The answer is yes. “My crime is curiosity,” I confessed.
This group of teenagers exhibits many of the characteristics that non-technical people typically associate with hackers. There is nothing they enjoy more than taking on the challenge of hacking. Additionally, they aren’t harboring any ill will. As a game, it’s more fun for them, but when faced with a choice between doing the wrong or right thing, they opted for the latter.
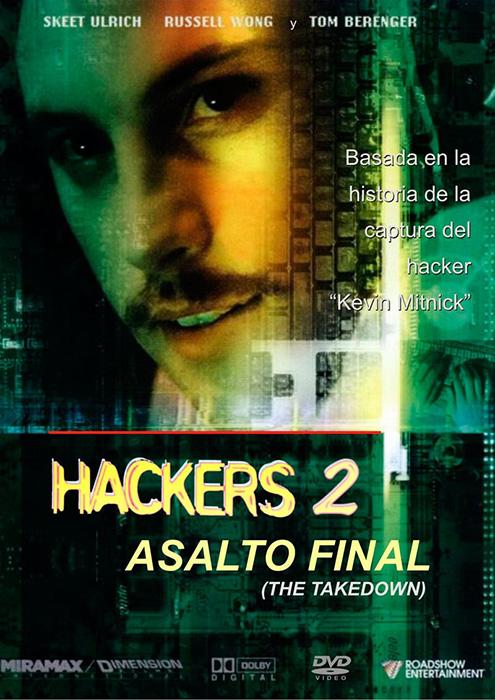
7. Takedown
Read More : 23 Best Movies Like Stranger Than Fiction That You Will Enjoy Watching Update 07/2024
Takedown is based on the true story of Kevin David Mitnick and Tsutomu Shimomura, a famed hacker and his nemesis. It appears in this hacking film that Mitnick was the bad guy and Shimomura was the good guy. However, the genuine tale may be more complicated than simply a black-and-white one. The film provides a very true depiction of the hacking world and its appeal to certain impulsive and savant-type individuals.
8. Tron
This is another early entry into the hacking genre, with a fantasy and science fiction storyline woven together. An ex-employee, Kevin Flynn, is attempting to hack his previous employer. However, he is thwarted by the system’s mainframe. It turns out that the computer is self-aware and power-hungry when other programmers try to access it. Trying to find proof that the corporation stole his ideas, Flynn is looking for evidence. Being infiltrated by the mainframe, he is then digitally transformed into one of the program’s components. Flynn is a character who isn’t all good or all bad, which makes him approachable to the audience. As far as I know, this sequence of him in the show is purely for amusement purposes (but who knows about the future).
9. The Fifth Estate
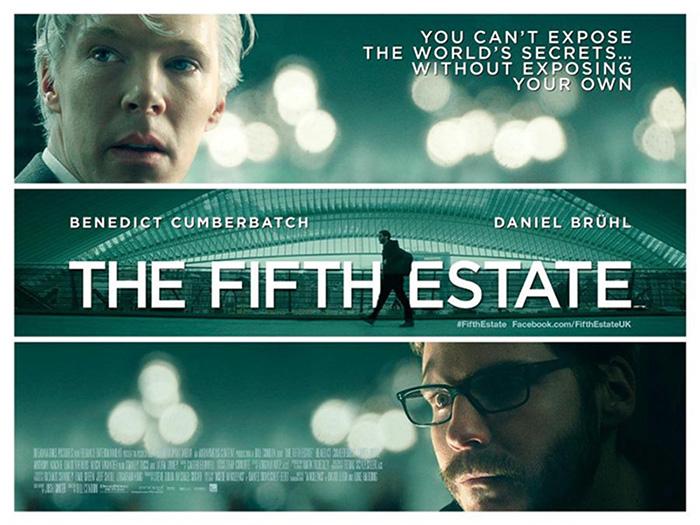
An unauthorized narrative of Julian Assange and WikiLeaks is presented in The Fifth Estate. An idealist and egotist, Julian Assange is shown in the film as an information leaker who is trying to bring about a better society. Prior to his arrest, Assange had an extensive list of systems that he had hacked into. These included the Pentagon, NASA, and Citibank, among others. Even if Julian Assange viewed his hacking as an act of internet activism, it did not make it any less unlawful. An account of journalist Daniel Domscheit-Berg, who began working with Julian Assange and eventually split with him because he believed him to be greedy and wicked, is the basis for this film.
10. Untraceable
They spend their evenings battling identity theft until an anonymous tip leads them to the website, KillWithMe.com, which is featured in Untraceable. The site’s creator intended it to be a failsafe. In the event that a server is unavailable, another server is quickly activated. In order to urge others to join him in killing, the hacker has created a website. He kidnaps, tortures, and eventually kills his victims based on the involvement of others. It is the public’s fascination with technology and online activities that this film truly focuses on (and this was even before the social media age). Even if the plot is a touch ridiculous, it makes anyone who utilizes technology on a regular basis think about how it can both benefit and harm.
Hacking Isn’t Just in the Movies
Our collection of hacker movies doesn’t necessarily reflect the real-life experience of a hacker. However, hacking talents can be put to use in the real world to have a positive impact. Despite the fact that you may not be chasing down serial killers and fighting artificial intelligence, as an ethical hacker, you may help preserve and safeguard the personal information and confidential data of millions.
When it comes to hacking, the best are those that have an inquisitive mind and are continuously looking for the answers. It’s important to be a white hat if you can keep up with the crooks or if you can catch up quickly. Information technology is constantly evolving and changing. Criminals feel the same way. As a result, society is in need of smart, quick minds capable of defeating black hat hackers.
A Certified Ethical Hacker (CEH) certification is required to do ethical hacking (CEH). In order to do this, you’ll need to take a course to prepare you for a test. Ethical hackers can learn about 18 of the most current security domains in Alpine Security’s pass-guaranteed CEH program. Over 270 attack methods are covered in the course’s 18 comprehensive courses. To learn more about our CEH class and the possibilities for an ethical hacking career, we encourage you to contact us.
Sources: https://www.lunchbox-productions.com
Categori: Entertaiment